Introduction
Fraud rarely begins with a dramatic act. It begins slowly, quietly, through small decisions that feel justified in the moment. A shortcut here. An exception there. A judgment made under pressure. Over time, those decisions accumulate, and the organization discovers that what once looked like a minor lapse has become a systemic issue. After nearly four decades of working in forensic accounting, governance, and fraud risk management, I have seen the same pattern again and again. Fraud does not start in spreadsheets. It starts in culture, in incentives, in structure, and in the behavior leaders signal, tolerate, or ignore.
As year-end approaches, these conditions intensify. Performance expectations tighten. Incentives concentrate. Executives feel pressure to deliver results. Operational teams work faster and with fewer resources. Controls are strained. Cultural cracks surface. And the elements of the Fraud Pentagon become more pronounced. Pressure rises. Opportunities expand as teams shift focus to deadlines. Rationalization becomes easier. Competence is misdirected. Arrogance tells individuals that oversight will not catch up.
This is the environment boards and audit committees must navigate. Year-end is when fraud risk is greatest. Compound the typical year-end pressures with economic headwinds and an evolving regulatory landscape, and you have the makings of a fraud perfect storm. Remember, where there’s confusion, there’s opportunity (but that opportunity can be for good or bad intentions). The purpose of this article is to help directors understand the real contours of fraud today and strengthen their ability to challenge management constructively and effectively. The perspective offered here combines insights from the 2024 ACFE Occupational Fraud report, the 2023 COSO Fraud Risk Management Guide, contemporary enforcement actions, behavioral ethics, the Five Board Dilemmas of 2025, and the critical thinking frameworks I have written about extensively, including the C² model. It also reflects observations drawn from investigations, risk assessments, governance failures and M&A integration breakdowns, including the structural oversight gaps underscored in the Millicom FCPA matter.
This writing is not intended to summarize fraud trends in broad strokes. It is intended to educate. It is designed to help boards understand not just what fraud looks like, but why it emerges and how oversight can meaningfully reduce risk.
Fraud Trends at Year End
Every year, organizations move into year-end with a familiar pattern. Attention concentrates on revenue recognition. This is understandable. However, revenue recognition mistakes or manipulations can distort financial performance, influence investor decisions, and attract regulatory scrutiny. Senior leadership often focuses on top-line performance, and external stakeholders place significant weight on the numbers reported during this period.
But year-end fraud risk is much broader than revenue recognition. The modern fraud landscape has shifted significantly. Fraud is increasingly decentralized, technologically enabled, third-party driven, and embedded in operational processes rather than financial reporting entries. Procurement environments, payroll operations, cyber interfaces, ESG reporting, government program administration, and mergers and acquisitions now present significant fraud risk. Boards must recognize that focusing solely on revenue recognition leaves them blind to the most common and costly schemes operating inside their organizations.
Fraud today is faster, smarter, and more adaptive. That is, the volume and velocity at which fraud schemes are escalating is outpacing entity risk and control evaluations. Fraud emerges in places where controls have not kept pace with technology, where oversight lags behind organizational change and where behaviors are shaped by pressure, cultural drift, and misaligned incentives. Boards must expand their field of view to govern fraud risk effectively.
Revenue Recognition: Still Important but No Longer the Most Frequent Scheme
Revenue recognition remains a central concern during year-end because of its potential to distort financial reporting. Examples include recognizing revenue prematurely, recording sales to customers who have not taken control of goods, or using informal side agreements to accelerate revenue. Channel stuffing remains a risk in industries where distributors or resellers are involved. The financial impact of these schemes can be significant, and regulators continue to scrutinize rounding anomalies, contract modifications, and manual journal entries that affect timing.
However, the broader view shows that revenue recognition fraud is not the most common scheme. According to the ACFE Occupational Fraud 2024 report, the vast majority of fraud cases involve asset misappropriation, not financial statement manipulation. Only a small portion involves revenue recognition, though those cases tend to have the highest financial impact. Most fraud occurs because internal controls were weak or overridden, and most fraud continues to be primarily detected by tips, not audits or management review.
The lesson for boards is clear. Revenue recognition remains high risk and must be monitored closely, particularly at year-end. But the most common fraud schemes occur elsewhere, often in operational areas that receive far less board attention. A singular focus on revenue recognition creates blind spots. Boards must broaden their oversight.
Vendor and Procurement Fraud: The Most Underestimated Organizational Threat
Vendor and procurement fraud has become one of the most widespread and financially damaging forms of fraud. These schemes are often subtle, operational in appearance, and deeply embedded in day-to-day processes. They flourish where procurement practices have not evolved at the same pace as technology and hybrid work. They also exploit gaps created by fragmented purchasing authority and inconsistent vendor verification procedures.
A few examples illustrate this clearly.
Fictitious vendors emerge when an employee creates a vendor using a plausible name, issues invoices for services never performed, and approves payment. Vendor creation is often decentralized and lightly monitored. Further, after a period of time, this schemes dollar impact becomes “baked” into budgets. As a result, these schemes can persist for years.
Collusive kickbacks occur when an insider works with a vendor to inflate pricing in exchange for personal benefit. Both parties share the illicit gain and neither has an incentive to report the misconduct. Without strong monitoring and periodic vendor reviews, these schemes are hidden within normal operations.
Altered payment instructions occur when fraudsters intercept or mimic vendor communications and instruct the organization to change bank account information. Without strong authentication controls, these schemes succeed with alarming frequency, particularly in hybrid work environments.
Duplicate billing or invoice splitting occurs when vendors submit multiple invoices for the same work or break invoices into smaller amounts to stay under approval thresholds. When oversight is fragmented or overwhelmed, these schemes blend into routine workflows.
Boards must recognize that procurement fraud is rarely about sophisticated manipulation of financial systems. It is about exploiting process gaps and human behavior. These schemes reflect three powerful elements of the Fraud Pentagon: opportunity driven by weak controls, competence in manipulating procurement processes and rationalization by individuals who believe the amounts are small or justified. Procurement fraud is a direct signal of deeper cultural and control issues, and boards must treat it as such.
Asset Misappropriation and Payroll Fraud: Small Steps, Big Consequences
Asset misappropriation remains the most common form of fraud worldwide. These schemes may begin small, but they grow quickly when ignored. They are particularly common in organizations where monitoring is inconsistent/nonexistent, where segregation of duties is weak, or where cultural norms tolerate minor policy violations.
Cash skimming occurs when employees receive payments from customers but do not record them. This is common in retail, hospitality, healthcare, and other cash-intensive operations. It erodes revenue, distorts financial reporting, and signals systemic weaknesses.
Ghost employees emerge when those with access create fictitious employee records and route wages to their own accounts. These schemes are often uncovered only when internal audit or external auditors perform detailed payroll reviews.
Expense reimbursement fraud emerges when employees submit personal, or fictitious, expenses as business-related. Without clear policies, manager accountability or auditing, these schemes expand rapidly and reflect deeper cultural issues.
Corporate card misuse occurs when employees use company cards for personal purchases and disguise them as legitimate business expenses. When review processes are weak, these schemes become embedded in the culture. Tip: You can block certain merchants by contacting your financial institution or credit card issuer.
Boards often underestimate asset misappropriation because it appears incremental or is rationalized away as immaterial. But it signals cultural tolerance of misconduct and often precedes larger frauds. When employees believe that small violations are acceptable, ethical drift accelerates. Asset misappropriation is not petty. It is predictive.
Cyber Enabled Fraud and the Evolution of Deception
Cyber fraud has transformed the fraud landscape. The evolution of artificial intelligence, synthetic identity creation and social engineering techniques has made it easier for criminals to manipulate individuals and systems. Fraud today is not limited to breaches or malware. It focuses on trust, relationships, and behavior.
Pig butchering schemes combine social engineering and investment fraud. Fraudsters build long-term relationships with victims, often over months, and then persuade them to invest in fraudulent platforms. These schemes are psychologically sophisticated and consistently effective.
Account takeover fraud occurs when criminals use stolen credentials to access financial accounts or payment systems. They study legitimate behavior patterns and replicate them, making detection difficult.
Deepfake executive impersonation relies on AI-generated audio or video to deceive employees into authorizing payments or releasing sensitive information. These schemes exploit trust in leadership and expectations around responsiveness.
Synthetic identity fraud combines real and fabricated personal data to create new identities used for credit fraud, tax fraud or access manipulation. These schemes bypass traditional verification systems.
Business email compromise continues to be one of the most financially damaging forms of cyber fraud. Fraudsters use spoofed communications to instruct employees to change vendor bank information or approve urgent payments.
Cyber fraud is not a technical problem. It is a behavioral problem. It exploits trust, urgency, authority, and the assumption that familiar requests are legitimate. Boards must evaluate cyber fraud as a human risk as much as a technology risk.
Government Program Fraud
Government program fraud has grown substantially due to relief funding, grant programs and rapid disbursement mechanisms. These schemes often begin with fabricated documentation, misrepresented eligibility, or inflated claims. They frequently intersect with vendor and procurement frauds and involve the same behavioral components: opportunity, rationalization, and weak oversight.
Examples include impersonating government officials to solicit payments, submitting fraudulent applications for loans or grants and inflating invoices for government-funded projects. These schemes require boards to understand not only financial controls, but the compliance frameworks surrounding government program participation.
ESG Fraud and the New Reporting Frontier
ESG reporting has become a focal point for investors, regulators, and stakeholders. With that visibility comes new fraud risk. ESG fraud occurs when organizations misrepresent environmental, social or governance performance, often because of pressure to meet expectations or perceived benefits associated with high ESG scores.
Examples include overstated emissions reductions, misrepresented diversity metrics, inflated sustainability achievements, manipulated carbon credits and understated environmental liabilities. These schemes reflect the same behavioral dynamics that drive financial reporting fraud: pressure to perform, opportunity created by complex reporting frameworks and rationalization based on perceived organizational benefits.
Boards must approach ESG reporting with the same rigor applied to financial reporting. ESG disclosures now drive capital allocation, stakeholder trust and regulatory compliance. They must be accurate.
Mergers and Acquisitions Fraud: The Overlooked Structural Risk
Mergers and acquisitions create immediate and significant fraud risk. The moment a deal closes, the organization inherits more than just assets. It inherits systems, controls, cultural norms, third party relationships and pre-existing vulnerabilities. Fraud risk often spikes during the integration period because oversight lags behind structural change.
As highlighted in recent enforcement actions, including the Millicom FCPA matter, organizations often fail to integrate compliance and structural oversight early enough. Acquired entities operate with legacy processes that do not align with the acquirer’s standards. Third party relationships remain unreviewed. Cultural norms go unaddressed. Without clear oversight, these inherited risks become embedded in the combined organization.
M&A fraud rarely begins with sophisticated accounting manipulation. It begins with weak onboarding, unclear responsibilities, and assumptions about inherited processes. When pressure combines with fragmented oversight, the elements of the Fraud Pentagon align almost perfectly.
Boards must expect management to perform immediate post-acquisition risk assessments, integrate governance structures early, review inherited third parties and establish clear oversight ownership. In M&A, fraud risk is not an abstract concept. It is a structural reality.
Behavioral Drivers of Fraud
Fraud is not driven solely by control failures. It is driven by human behavior. Behavioral science explains why misconduct emerges even in organizations with strong policies and procedures.
Bounded ethicality occurs when individuals make decisions without fully considering ethical implications. They focus on outcomes, deadlines, or personal incentives rather than broader consequences.
Motivated blindness emerges when people overlook wrongdoing because acknowledging it would create conflict, disrupt relationships, or challenge financial performance narratives.
Ethical fading occurs when the ethical dimension of a decision becomes less visible. Individuals frame decisions as business choices to the exclusion of ethical considerations or impacts.
Incrementalism, often called the “slippery slope,” happens when small deviations lead to larger ones. What begins as a small exception becomes normalized and eventually expands into significant misconduct.
Hubris and overconfidence contribute when individuals believe controls do not apply to them or assume they can manage risks without consequences.
Boards must recognize that fraud emerges from these behavioral drivers. Controls are essential, but without attention to culture, leadership behavior and incentive structures, and training, controls alone are insufficient.
COSO 2023 Applied to Fraud Risk Management
COSO’s 2023 Fraud Risk Management Guide outlines clear expectations for organizations, but the value lies in its application. Yes, I am constantly referring to this document because it is a treasure trove of information and guidance.
Continuous fraud risk assessments require organizations to update their understanding of fraud risks regularly. Fraud risk is not static. It changes with mergers, new products, new systems, new market conditions and new regulatory standards. Organizations must use internal incident data, audit findings, investigation outcomes and external enforcement trends to refine the risk assessment continually.
Aligning controls with changing business models requires organizations to reassess objectives, risks, and controls whenever they make structural changes. For example, shifting to a digital procurement system requires evaluating objectives, new risk, and new controls, not simply transplanting old controls into new technology. Controls must be designed for the actual operating environment.
Strengthening monitoring mechanisms requires organizations to review key indicators and exception reports regularly. Monitoring is not an annual event. It is a continuous process that includes data analytics, exception reporting and timely investigation of anomalies.
Documenting ownership of fraud risks ensures someone is accountable for monitoring, managing, and reporting on specific risks. Ownership creates clarity and prevents the diffusion of responsibility. When everyone is responsible, no one is responsible.
Integrating fraud into enterprise risk management ensures fraud risk is considered in strategic planning, market expansion, acquisitions, technology adoption and major operational changes.
Evaluating culture requires more than reviewing policies. Boards should expect evidence from employee surveys, hotline metrics, investigation outcomes and disciplinary actions. Culture is demonstrated through behavior.
The Marks C² Model and Board Oversight
The C² model emphasizes six critical thinking behaviors that strengthen board oversight.
Curiosity requires directors to ask deeper questions. It moves the board away from accepting high-level assurances and toward engaging management in meaningful dialogue.
Courage allows directors to challenge assumptions, question optimistic narratives and ask difficult questions even when the answers may be uncomfortable to leadership.
Context provides the environment surrounding decisions. When pressure is high and/or resources are strained, fraud risk increases. Directors must understand context to evaluate risk accurately.
Cognition addresses bias. Directors must recognize when they are giving undue weight to past success or personal relationships. Cognition requires self-awareness.
Cross examination tests the consistency of information across time and across functions. Directors should compare statements from management with findings from internal audit or compliance.
Corroboration confirms information through independent evidence. Boards should seek data, testing results, investigation outcomes and analytics to support management’s assertions.
Applied consistently, the C² model strengthens oversight and improves the quality of decisions made by boards.
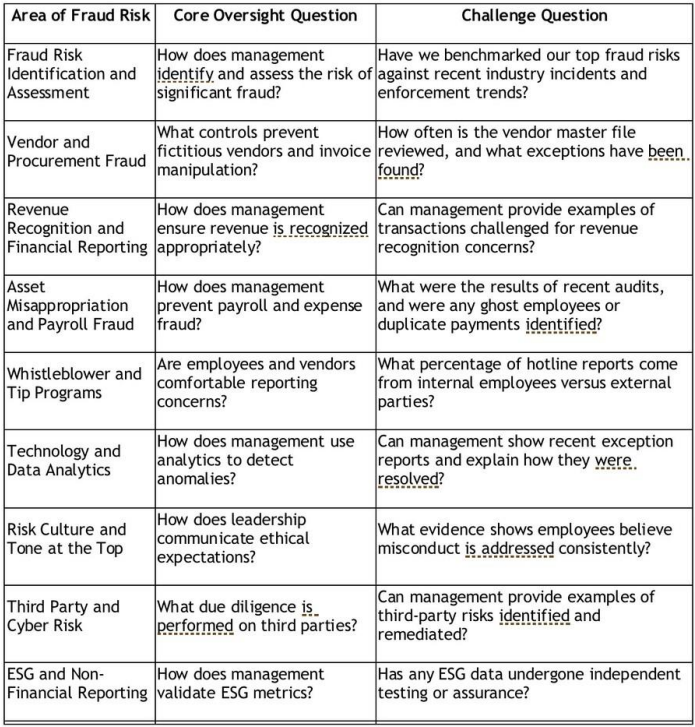
Sample Board Oversight Questions and Challenge Questions
Closing
Fraud risk continues to evolve. While revenue recognition remains important, it is only one part of a much larger landscape. The most common and costly fraud schemes today occur in procurement, payroll, cyber environments, and third-party ecosystems. These schemes are shaped by modern operating models, technological advances, behavioral dynamics, and cultural signals.
Boards must adopt a broader and more sophisticated approach to oversight. They must integrate critical thinking, behavioral insights, COSO expectations, structural oversight in M&A and the Fraud Pentagon into their understanding of fraud risk. Controls matter, but without attention to culture and behavior they are insufficient. Oversight must be active, curious and evidence driven.
Fraud does not emerge overnight. It builds through small decisions, subtle signals and ignored warning signs. Boards that remain engaged, informed, and willing to challenge management will identify these signals early and protect the organization from preventable harm.
Embrace discourse and differing opinions. Wrestling with difficult topics and opposing views leads to the recognition of risks, weaknesses, and opportunities. This drives innovation and better solutions. That is, focus on Thinking – Critically and Creatively.
Think about this…
Fraud does not grow in the shadows. It grows in the cracks where no one is checking or asking questions. Strong governance is built not on certainty, but on curiosity, courage, and a commitment to understanding the human and structural conditions that allow misconduct to take hold.
Happy Thanksgiving!
Fraud Tip Friday
Weekly Insights on Governance, Risk, and Compliance
Fraud Tip Friday is a blog dedicated to delivering practical insights into governance, risk, and compliance (GRC), with a special focus on fraud risk management and investigations. Each edition explores real-world challenges, emerging trends, and actionable strategies to strengthen organizational integrity and resilience.
Purpose
The goal of Fraud Tip Friday is to empower professionals in audit, compliance, and risk management roles with concise, applicable knowledge that enhances their ability to detect, prevent, and respond to fraud.
Key Themes
- Fraud Risk Management: Frameworks, controls, and best practices for identifying and mitigating fraud risks.
- Investigations: Techniques for conducting effective internal investigations, evidence gathering, and reporting.
- Governance: Strengthening oversight structures and ethical culture to reduce vulnerabilities.
- Compliance: Aligning policies and procedures with regulatory expectations and industry standards.
- Emerging Threats: Insights into new fraud schemes, digital risks, and evolving compliance landscapes.
- Regulatory Developments: Analysis of recent enforcement actions, policy updates, and regulatory decisions that shape the governance, risk, and compliance environment.
Each Friday, the blog features:
- A focused fraud prevention or investigation tip.
- A short case study or scenario illustrating the concept.
- Practical takeaways that can be applied immediately within organizations.
- A review of recent enforcement actions or regulatory updates relevant to fraud and compliance professionals.
Fraud Tip Friday serves professionals in:
- Internal audit
- Risk management and corporate governance
- Compliance
- Public and private organizations
- Legal and investigative roles
- Board roles
Mission
To foster a culture of transparency, accountability, and ethical decision-making by equipping professionals with the tools and insights needed to stay ahead of fraud risks and regulatory changes.


