During the 2025 National Day holiday, a decision from the Irish Data Protection Commission across the ocean sparked widespread attention. Although the decision was made long ago, what are the reasons behind it? Why did TikTok's defense fail? What is the impact of this decision for China-EU cross-border data transfers? Through summarizing, concluding, and preliminary analysis of the recently published decision document, we have specially written this article, hoping it will be helpful to all enterprises or relevant institutions involved in China-EU cross-border data transfers.
I. Overview
According to the decision, the core of the investigation by the Irish Data Protection Commission (DPC) was that when TikTok Ireland transferred the personal data of European Economic Area (EEA) users to China, it failed to ensure that the personal data received a level of protection essentially equivalent to that within the EU. The DPC ruled that TikTok Ireland violated Article 46(1) of the General Data Protection Regulation (GDPR) because the Standard Contractual Clauses and supplementary measures it relied upon were insufficient to address the risks of access by public authorities under Chinese law. Furthermore, the DPC also found that TikTok Ireland violated the transparency obligations under Article 13(1)(f) of the GDPR by failing to adequately inform users of the details and risks of the data transfers. Ultimately, the DPC's administrative penalties included the suspension of cross-border data flows, an order to bring processing activities into compliance, and an administrative fine of up to 530 million euros.
II. Core Issue: Whether Remote Access Constitutes Cross-Border Transfer
The DPC's decision is based on a crucial legal interpretation: remote access to personal data by personnel in a third country itself constitutes a "transfer" as defined in Chapter V of the GDPR.
Although this interpretation is a consensus in all cross-border data compliance, for corporate legal departments explaining compliance logic to business units, the DPC's finding can be directly cited: if an enterprise stores EEA user data on servers in Singapore, the United States, or even within the EEA, but its global support or development teams (for example, teams in China) can still remotely access this data. Regardless of where this data is stored globally outside of China, such as in Singapore, when an employee located in China views or processes that data, this action means the data is being processed on a computer information system within China. Therefore, this constitutes a cross-border transfer under the GDPR, and the enterprise's compliance obligations must be fulfilled.
The physical location of data servers is no longer the determinative factor in the analysis of data transfers. The regulatory focus has irrevocably shifted to the location of the personnel who can access this data.
One of TikTok's main defenses relied on the "territoriality principle" of Chinese law. It argued that since the data was not physically stored within Chinese territory, the Chinese government lacked the legal authority to compel its production.
However, the DPC did not accept this, believing that TikTok failed to provide any specific evidence or legal precedent to demonstrate that this principle effectively protects personal data from access requests under relevant laws (such as the National Intelligence Law, the Counterespionage Law). According to the principles established in the Schrems II case, the data exporter faces the burden of proof to "verify, safeguard, and demonstrate" that the data receives a level of protection essentially equivalent to that in the EU. TikTok's failure to fulfill this responsibility is the core reason for its violation of GDPR Article 46(1).
This involves an interesting hypothesis: if personnel located in China only access the data without performing any storage or other actions, would it still constitute the aforementioned "threat"? After reading the decision, we believe the DPC's logic is clear: current internet remote access technology will certainly leave caches and cache files; this is not only a standard mechanism but also a way to improve the efficiency of subsequent access. Unless the company's solutions and defenses can eliminate the concerns regarding access permissions, they will be unable to alleviate the worries of EU regulators.
III. As Long as Access is Not Restricted, Supplementary Measures Are Difficult to Establish
The DPC decision indicates that if the issue of access permissions is not fundamentally resolved, technical and contractual measures cannot remedy the fundamental flaws in the cross-border data transfer framework.
Why Encryption Measures Were Deemed Ineffective
TikTok implemented technical measures, including encrypting data in transit and at rest. This is standard industry best practice.
However, the DPC ruled this measure ineffective. The key flaw is that, in order to perform their core job functions (such as R&D, content moderation, technical support), authorized employees located in China needed to access the data in a decrypted state or in plaintext form.
Once the data appears in plaintext on a system in China, it is fully exposed to what EU regulators call the "risk of access requests from the Chinese government based on its domestic law." In that case, encryption measures at the point of data use cannot provide any so-called "effective protection."
The Limitations of Contractual Safeguards
The main compliance measures TikTok relied on for cross-border data transfers were Standard Contractual Clauses (SCCs), as well as legally required internal and external compliance measures. The DPC believes that these measures are contractual in nature. They can bind the relevant corporate entities but have no legal effect on state authorities. The cross-border data transfer contract between TikTok Ireland and its Chinese parent company cannot override orders issued pursuant to enforceable laws, regulations, or decisions.
It can be seen that this decision is largely consistent with the Schrems II case and subsequent guidance from the European Data Protection Board (EDPB). These prior decisions or guidance documents clearly state that if the laws of the destination country would undermine the effectiveness of contractual commitments, then SCCs alone are not sufficient.
IV. The Data Cross-Border Transfer Standard Set by the Schrems II case
We understand that the TikTok decision is not an isolated case but rather a necessary extension of the high compliance standards set by the Court of Justice of the European Union (CJEU) in the Schrems II case.
Direct Application of the "Essentially Equivalent" Test
The Schrems II case not only invalidated the EU-US "Privacy Shield" agreement but also established that when using SCCs for data transfers, a case-by-case assessment must be conducted to ensure the destination country provides a level of data protection "essentially equivalent" to that of the EU.
The DPC's investigation is a "correct" extension of this judgment's logic. Even TikTok's own Transfer Impact Assessment(TIA) admitted that relevant Chinese laws have "substantive differences from EU standards." This is the most difficult point for any enterprise to prove: how to fully assess the differences between these legal systems in a specific cross-border transfer scenario (i.e., remote access), and what effective measures the enterprise can implement to offset the risks created by these differences.
The Importance of the TIA
The decision shows that a TIA cannot be a general and highly generalized document. It must be specific, contextual, and rigorously documented.
Enterprises can no longer simply claim that the risk of government access is "low" or " theoretical." They must provide evidence and reasonable analysis to demonstrate that the specific data they transfer can be effectively protected in the specific operational scenario.
The DPC's focus on the "practical application" of Chinese law, not just the letter of the law itself, also sets a very high standard for enterprises drafting their TIAs.
V. Compliance Implications of This Case
Stringent Transparency Requirements
Another important part of this decision is the 45 million euro fine for violating the transparency obligations of GDPR Article 13(1)(f). TikTok's 2021 privacy policy was deemed insufficient because it failed to clearly identify China as a destination country for data transfers and failed to clearly describe the nature of the transfer (i.e., remote access by employees in China).
The lesson here is very clear: enterprises must be extremely honest with users. Vague statements such as "data may be transferred outside the EEA" are no longer sufficient. Privacy notices must clearly state which non-adequacy decision countries the data will be accessed by and explain the method and reason for the access.
Derogations Are Not a Viable Alternative
The DPC rejected the possibility of applying GDPR Article 49 derogations (such as contractual necessity or user consent) in such transfers.
The reason is that these derogations are only applicable to occasional, non-repetitive transfers. They cannot be used to legitimize systematic, repetitive, and routine data transfers that are core to a business model, which is precisely TikTok's operational structure. This conclusion closes off a potential compliance route that enterprises might have utilized.
Data Localization is Far from Sufficient
From this case, the practice of setting up data centers in Singapore or the EU for data localization storage, while keeping core operations in China, has become a huge risk for enterprises. Data localization does not alleviate the core concerns of EU regulators unless the enterprise can ensure that personal data cannot be accessed in plaintext or achieve a full localization of operations, among other aspects.
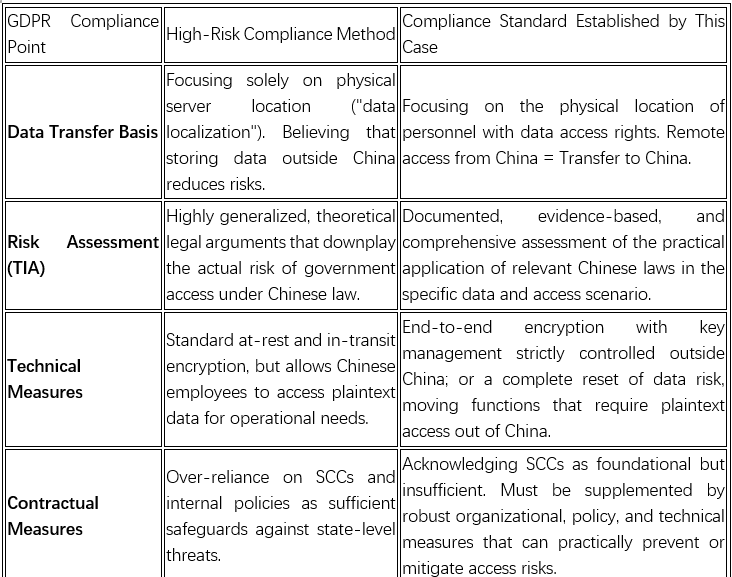
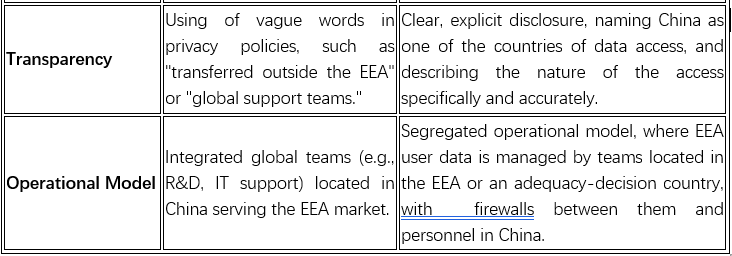
VI. Comparison of Key Compliance Points in This Case
VII. Three Major Issues Arising from This Case
Can Technical Measures Address the EU's Fundamental Concerns?
This decision effectively places China in the "high-risk" category for data transfers under the EU framework. To achieve legality, the data importer (the Chinese entity) must be technically unable to provide plaintext data to its own government. This may point to a "zero-knowledge" or "zero-trust" architecture, which becomes the only viable technical supplementary measure.
The logic behind this is:
- Access to plaintext data by Chinese employees is unacceptable to EU regulators.
- This means that standard encryption schemes where the service provider or its employees hold the decryption keys are no longer acceptable supplementary technical measures.
- A possible solution is for the data exporter (the EU entity) to exclusively hold the decryption keys, while the data importer (the Chinese entity) can only process encrypted data from start to finish. This is often referred to as "Bring Your Own Encryption" or client-side key management end-to-end encryption.
- However, this architecture is fundamentally incompatible with many common business operations that require plaintext access (such as content moderation, data analysis, or technical support).
Therefore, the decision forces enterprises to face a stark choice: either fundamentally re-architect their systems into a "zero-knowledge" model or stop performing those data-intensive business and commercial models for EEA data within China.
Does the "Data Localization" Model Need to Shift?
This decision fundamentally reshapes the compliance logic of "data localization." The future compliance focus for enterprises will no longer be the physical location of servers, but the geographical distribution of personnel who can access the data.
The evolution derived from this case is clear:
- In the past, the common compliance strategy for enterprises was to establish data centers in "safe" locations like the EEA or Singapore to build a physical barrier.
- The DPC's decision clearly states that regardless of where the server is located, remote access by Chinese employees places the data under the jurisdiction of Chinese law.
- This means that the "location" where the data processing activity occurs is now determined by the geographical location of the person accessing the data at the moment of access.
- Therefore, the IT architecture of a globalized company and its human resources and operational structure are now inseparable in the context of GDPR compliance. Global collaborative business models are now inherently high-risk.
- The final conclusion may be: true data localization requires not only local storage but also localized operational control, and access rights must be separated from personnel in high-risk third countries via a firewall. This poses a huge challenge to the cost, efficiency, and global business models of enterprises.
Have the Risks Arising from Cross-Border Data Transfers Transcended Purely Legal Issues?
Looking beneath the surface, we believe that this case reflects not just a technical data protection issue, but the inevitable result of the core incompatibility of laws and policy-making between different countries and legal jurisdictions. The enforcement of the GDPR has, to some extent, become a de facto foreign policy tool to promote the EU's legal and ethical norms globally.
The pattern of this trend is evident:
- The core of the Schrems II case was aimed at relevant US laws (such as FISA 702, E.O. 12333). The subsequent ruling against Meta reaffirmed this stance against the United States.
- This ruling against TikTok is the first time the same logic has been applied to China.
- In both cases, the core legal dispute is identical: the destination country has laws related to national security, and these laws authorize governments and other public authorities to extensively access personal data from the EU in the absence of standards that meet EU requirements.
Therefore, GDPR compliance is no longer just a matter for lawyers, data protection officers, or even the enterprises themselves; it is now closely linked to geopolitics, international relations, and the global expansion strategies of enterprises. Enterprises are being forced to make choices amidst huge global regulatory divergences.
VIII. Conclusion
The Irish DPC's decision against TikTok is not an isolated event but a new baseline for GDPR enforcement against China. Even though TikTok has already appealed this case to the Court of Justice of EU, it is clear from the Schrems II case that without inter-governmental negotiations on the relevant issues, the final outcome will be as expected.
For Chinese enterprises expanding overseas, particularly those entering the EU market, the final result of this case will have significant compliance implications: the traditional compliance model for going abroad will be greatly challenged; it is no longer a purely legal task but needs to be achieved through verifiable technical and organizational isolation.
It can be foreseeable that the time for a structural and operational transformation in overseas expansion has arrived.




